What is split tunneling?
Buckle up! Embark on our 5-part series and learn all about split tunneling, a Mullvad VPN feature now available on three platforms! In Part 1 (out of 5), we explain what split tunneling actually is.
Now that our app supports split tunneling on Windows, Android, and Linux, we’re excited to share our development journey with you. Written by one of our very own developers, this series will get somewhat technical as we go along, but for now let's take a brief moment to explain what split tunneling is.
What is split tunneling?
When using a private VPN, all internet traffic is typically sent in an encrypted VPN tunnel. This is a good default configuration that ensures traffic will not unexpectedly leak out unencrypted. However, using an encrypted tunnel in certain scenarios is too inefficient or simply not possible.
As a privacy-conscious person, it’s best to use the VPN tunnel as much as possible and only make exceptions for certain traffic. This is exactly what split tunneling does: it conditionally sends traffic outside the encrypted tunnel.
Different implementations of split tunneling will use different conditions in order to identify traffic that should be excluded. We've chosen to use a single condition: the application making the network request. And we’ll explain our solution more thoroughly later on.
How do I use Mullvad’s split tunneling feature?
The feature is currently available on Windows, Android, and Linux versions of the Mullvad VPN app.
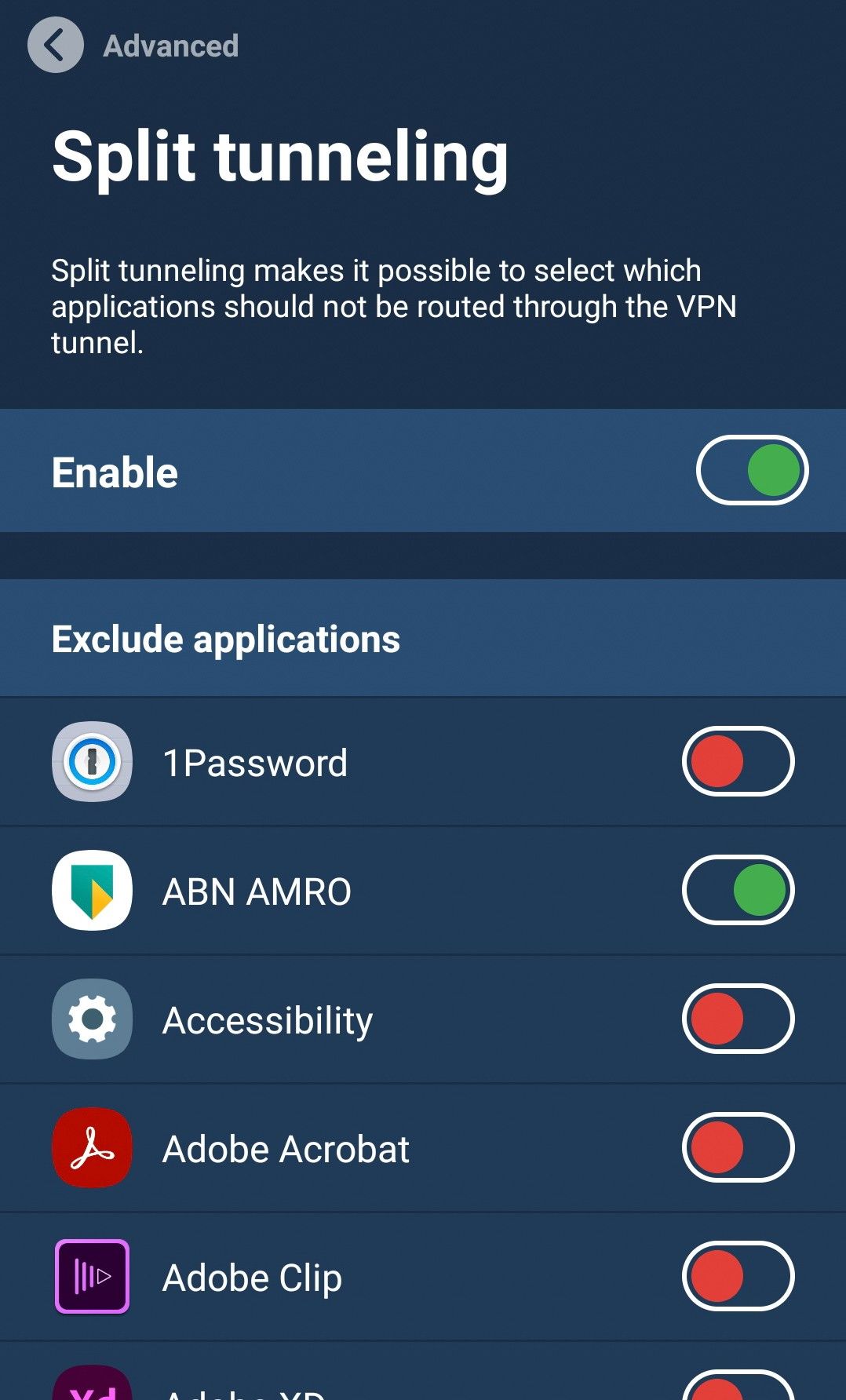
You can find the setting under Settings > Advanced > Split tunneling. Platform-specific details can be found in our split tunneling guide.
Up next
This article is in a five-part series on split tunneling – all written by a Mullvad developer. Stay tuned for the next installment which will discuss when split tunneling is useful.
- What is split tunneling? (this article)
- When is split tunneling useful?
- The limitations of split tunneling
- Can split tunneling be leaking traffic?
- Foundations of secure split tunneling
For the universal right to privacy,
Mullvad VPN